Cybersecurity - The Bigger Picture (2/n)
(I guess)
Connecting the dots.
So now that we know the history of the most fundamental concept of cybersecurity, how did we end up here in our world right now, whether you work as security analyst, security engineering, pentester, etc.?
As you know technology are evolving overtime. Kind of scary and fascinating at the same time that we don’t know full percentage of the history as well as the what might future bring. But back then its easy to be a hacker since they are just writing things down in a clay tablet. Its funny to imagine destroying their abacus and stating you’ve hacked their computer (nobody laughed? oof. tough crowd.). But essentially you’ve hindered the CIA triad, especially the Availability one.
Earlier times still used various methods in protecting information. Physical protection is one, substitutions and transposition ciphers to encode messages, seals and signatures, coded language, sometimes its just trust (nothing could go wrong, right?). So adversaries back then often involve espionage (spies), codebreakers (Alan Turing), social engineering, unauthorized access to physical spaces. I’d say these were the hackers of the low-tech age, since by definition a hacker is someone who can obtain data via unauthorized means.

New inventions were being developed as centuries past by, and it gets trickier to protect it. One notable device was the telegraph. Skilled individual can wire tap telegraph signals and obtain information. Then the 20th century came. Digital systems became more prevalent, and so does the security issues within it. We are talking about phreaking (Kevin Mitnick, RIP), malware and viruses (Elk Cloner and Morris Worm), and other crazy stuff.
But wait, pause. There’s malware during 1982? But the Internet was launched in 1983, right?
Spread in a floppy way. Yep.
Anyhow prior to January 1, 1983 computers were extremely introverted. They don’t know how to talk to other computers so attack vectors were limited to storage devices being plugged in. Easy to protect, right? As TDR analyst I might not be necessary at that point. Usage of computers in 1960s were to automate business transactions, freaking sent people outside Earth (Apollo 11 was coded in Assembly!) and other amazing things. They can protect these machines since they are practically isolated and cannot be accessed, yep you guessed it. Internet.
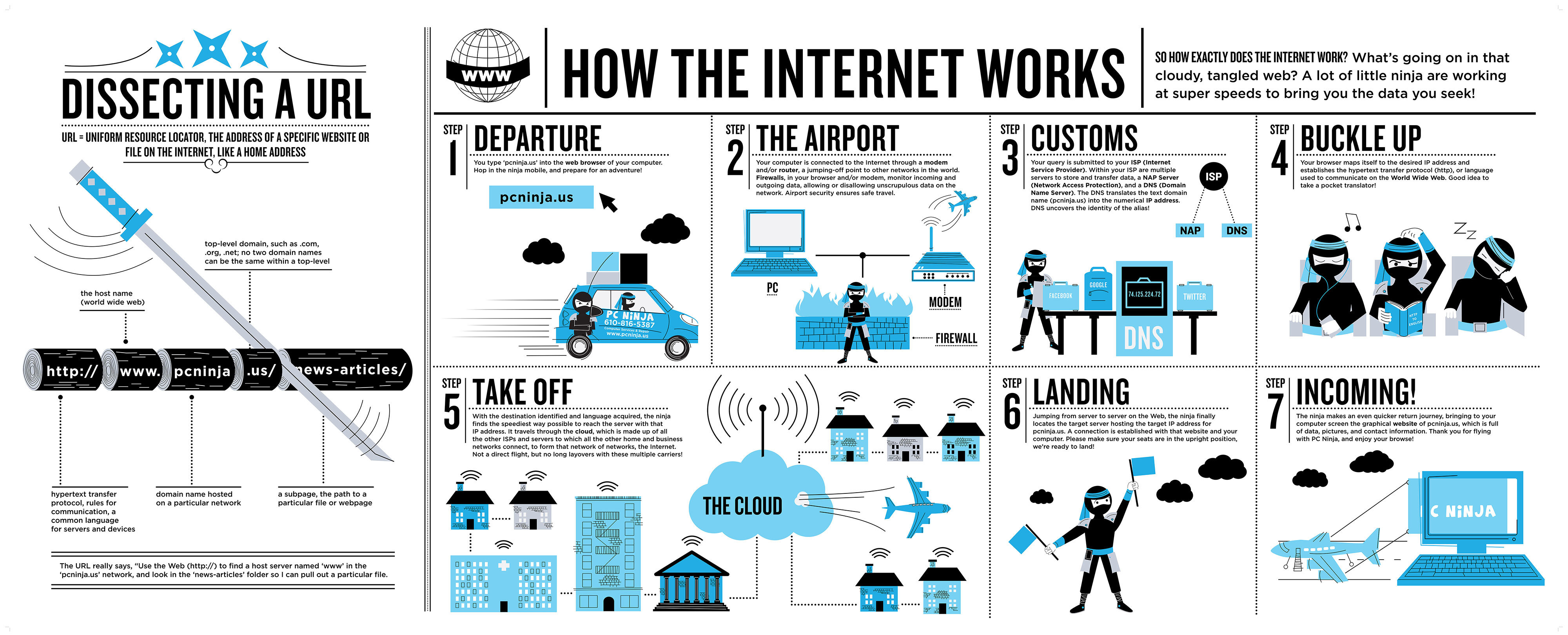
This is the most tricky part, the computer’s ability to communicate with other computer anywhere. ARPANET was one of the earliest wide-area networks and the predecessor of the internet. ARPANET have limited ability to scale and lacked the standard protocols for interconnecting different networks hence they created TCP/IP or the Transmission Control Protocol/Internet Protocol.
Think of it as the postal system:
- IP addresses are like physical addresses on envelopes, uniquely identifying the destination of a letter (or data packet) on the internet.
- TCP is like the postal service, ensuring that letters (or data packets) are reliably delivered to their destinations. It provides mechanisms for error checking, retransmission of lost packets, and sequencing to ensure that data arrives intact and in the correct order.
- Routing is like the network of postal routes and sorting facilities that determine the most efficient path for delivering letters (or data packets) from the sender to the recipient.
- The layered architecture of TCP/IP is akin to the different components of a postal system, such as post offices, sorting centers, delivery trucks, and postal workers, each performing specific functions to facilitate the delivery of mail.
- Just as the postal system enables communication between people across geographical distances, TCP/IP facilitates communication between devices on the internet, allowing data to be transmitted reliably and efficiently across networks.
This analogy also works (obtained from PC Ninja. Credits to the authors: Abby Ryan Guido, Andrew Shearer)
My key takeaway is that I might just stand in a corner with nothing to do if I was alive that time since basically they just trust??? each other?? to not hack them?? I mean up until 1970s or early 80s I guess.
But truth be told, security analysis and investigation started when government and military agencies were getting infected. They needed to investigate how they were infected thus creating some sort of procedure on how to tackle intrusion. (Btw, this happened in the early times of the internet. Yeah, see there are benefits if you remain introverted. Also as long as you don’t give a flop. Heh.)
So just quick maths here, computer + internet = my job is secured ($_$)
tl;dr
As we move forward from low-tech, to analog, to digital age, more ways are being develop to protect the Confidentiality, Integrity, and Availability of information. Also more ways to destroy it.
Here’s part 3.